The Problem: Identity Is the New Attack Surface
Cybersecurity has shifted. Attackers are no longer breaking in—they’re logging in.
Compromised credentials, session cookies, and identity-based access are now the primary entry points into organizations. Industry data continues to show that identity-related attacks—especially phishing and credential theft—remain the most common initial access vector, often going undetected for months.
By the time credentials appear on the dark web or trigger an alert, the damage is already underway. Security teams are left reacting.
According to the FBI Internet Crime Complaint Center, cybercrime continues to rise year over year, with billions in reported losses.
Identity-based attacks—particularly:
- Phishing
- Business Email Compromise (BEC)
- Credential Theft (InfoStealer)
remain among the most reported and financially damaging threats.
This is the PreBreach gap — the window between when a user is compromised and when the organization becomes aware.
For example, A U.S.-based organization was breached and reported on March 31, 2026. Figure 1 illustrates the timeline of the incident.
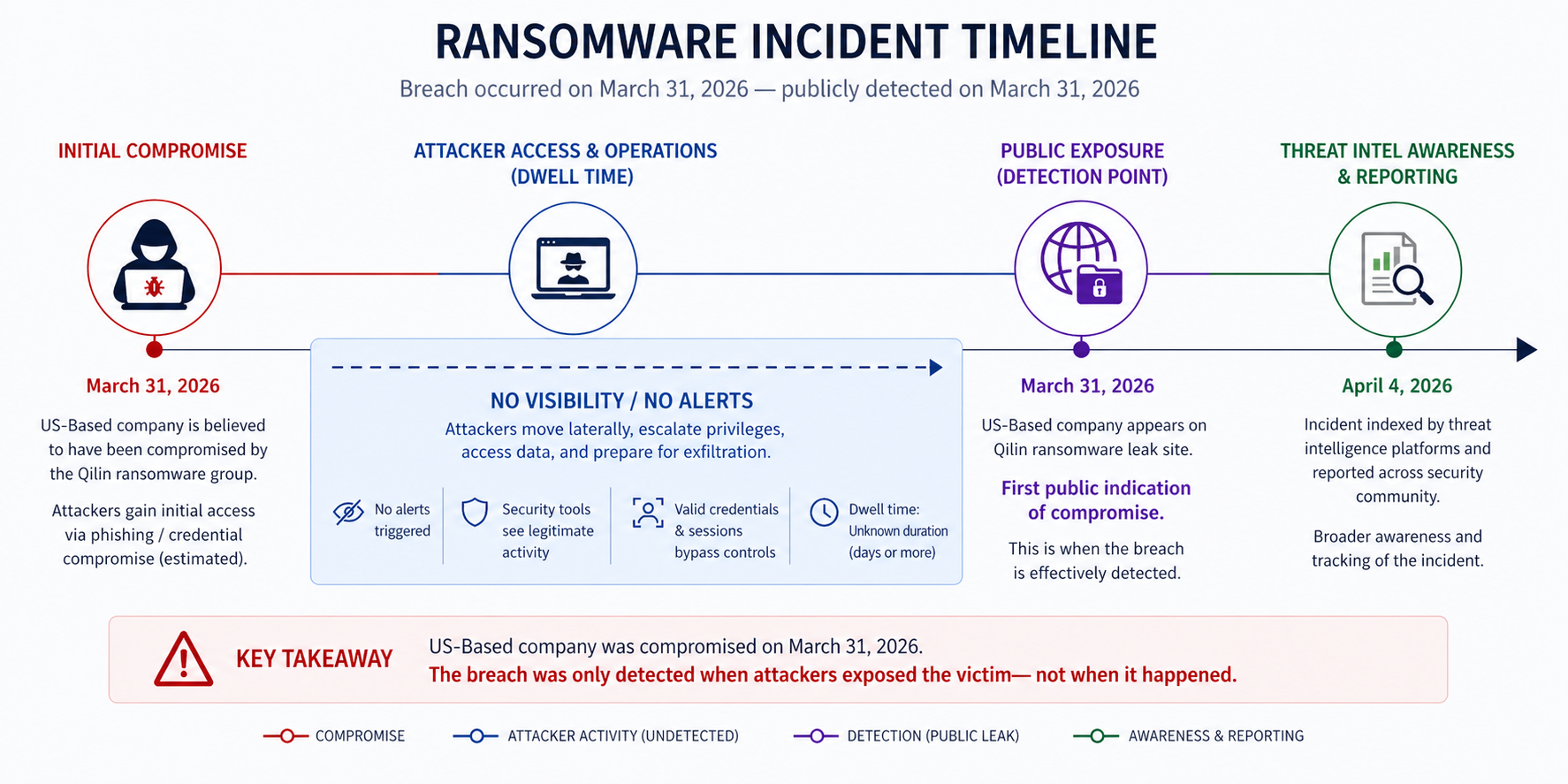
Figure 1: U.S.-based Organization Breach Timeline
From the incident, it shows that compromised accounts often go unnoticed until a breach occurs, typically identified during post-incident investigation. Without a ransomware event, attackers could maintain access for months or even years.
A New Approach: PreBreach Protection
At CyberArmor, we believe detection is no longer enough.
Our PreBreach intelligence identifies compromised credentials days and months before they surface on the dark web, giving organizations a critical window to act early.
This intelligence powers our latest solution:
PreBreach Identity Guard
PreBreach Identity Guard is a managed SaaS platform designed to proactively defend organizations against identity-based threats on Microsoft's cloud—before they escalate into breaches.
It is designed for modern environments where identity is the perimeter and response speed determines impact. Figure 2 illustrates how PreBreach Identity Guard operates.
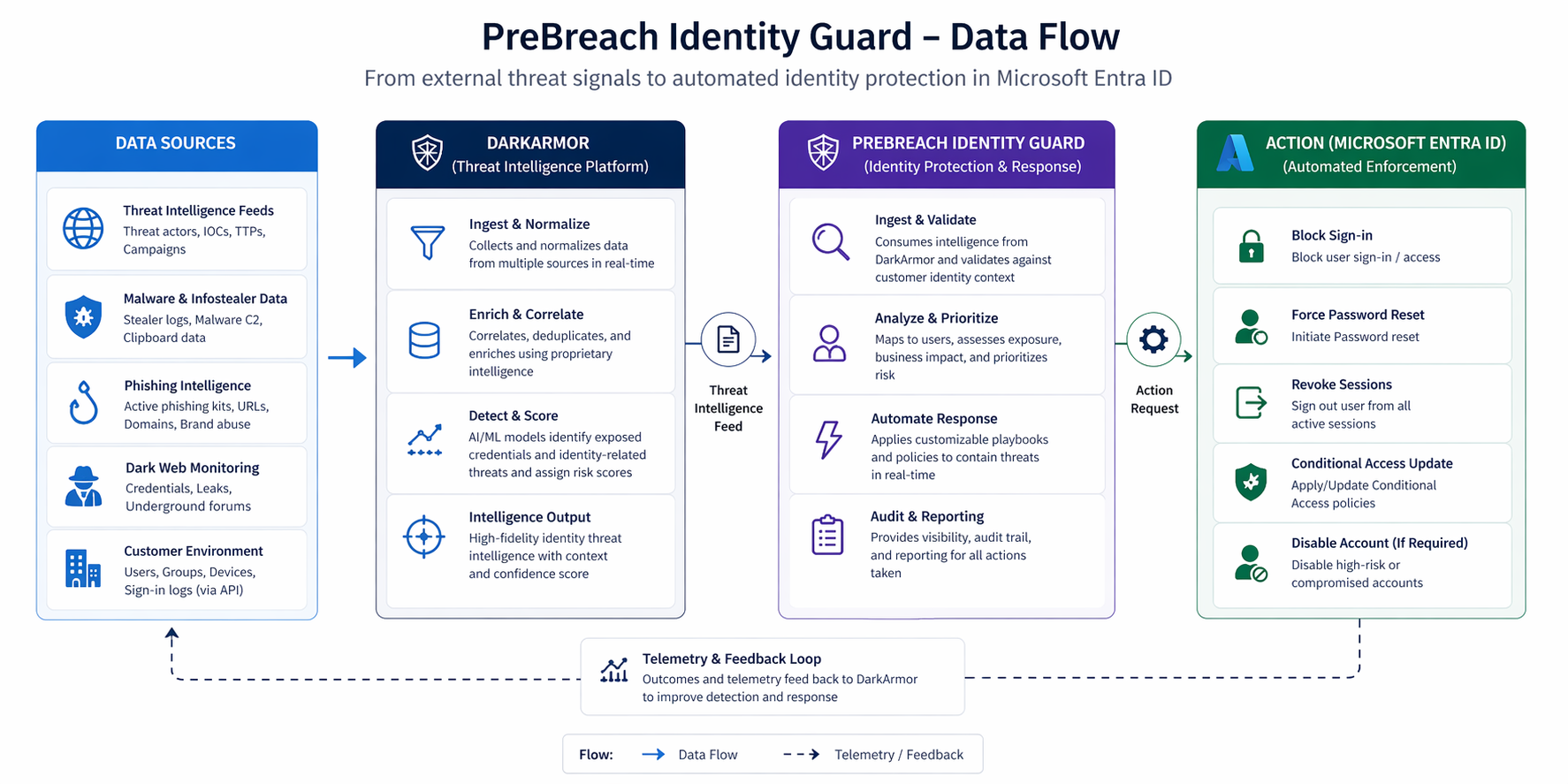
Figure 1: PreBreach Identity Guard
What Makes It Different
1. From Detection → Immediate Action
Traditional tools generate alerts, PreBreach Identity Guard turns findings into real-time containment actions across your identity environment (e.g., Microsoft Entra ID).
2. Continuous Monitoring Across Active Threats
The platform continuously analyzes exposure across:
- Active phishing campaigns
- Malware and infostealer logs
- Threat intelligence sources
- Dark web signals
This provides visibility into risks while attacks are still active, not after.
3. Automated Remediation
When a compromised identity is detected, PreBreach Identity Guard:
- Initiates remediation workflows
- Reduces dwell time
- Prevents account takeover and lateral movement
This shifts security teams from reactive investigation to automated protection.
Why It Matters
A compromised identity is not just a security issue—it is a business risk.
- Financial fraud
- Data exfiltration
- Supply chain compromise
- Brand damage
Attackers exploit the gap between compromise and detection. PreBreach Identity Guard closes that gap.
Based on the our incident example, we detected a compromised account on March 21, 2026 at 3:45:10 PM EST from a phishing attack. This occurred ten days before the breach was reported. Figure 3 illustrates how PreBreach Identity Guard detects and mitigates the threat.
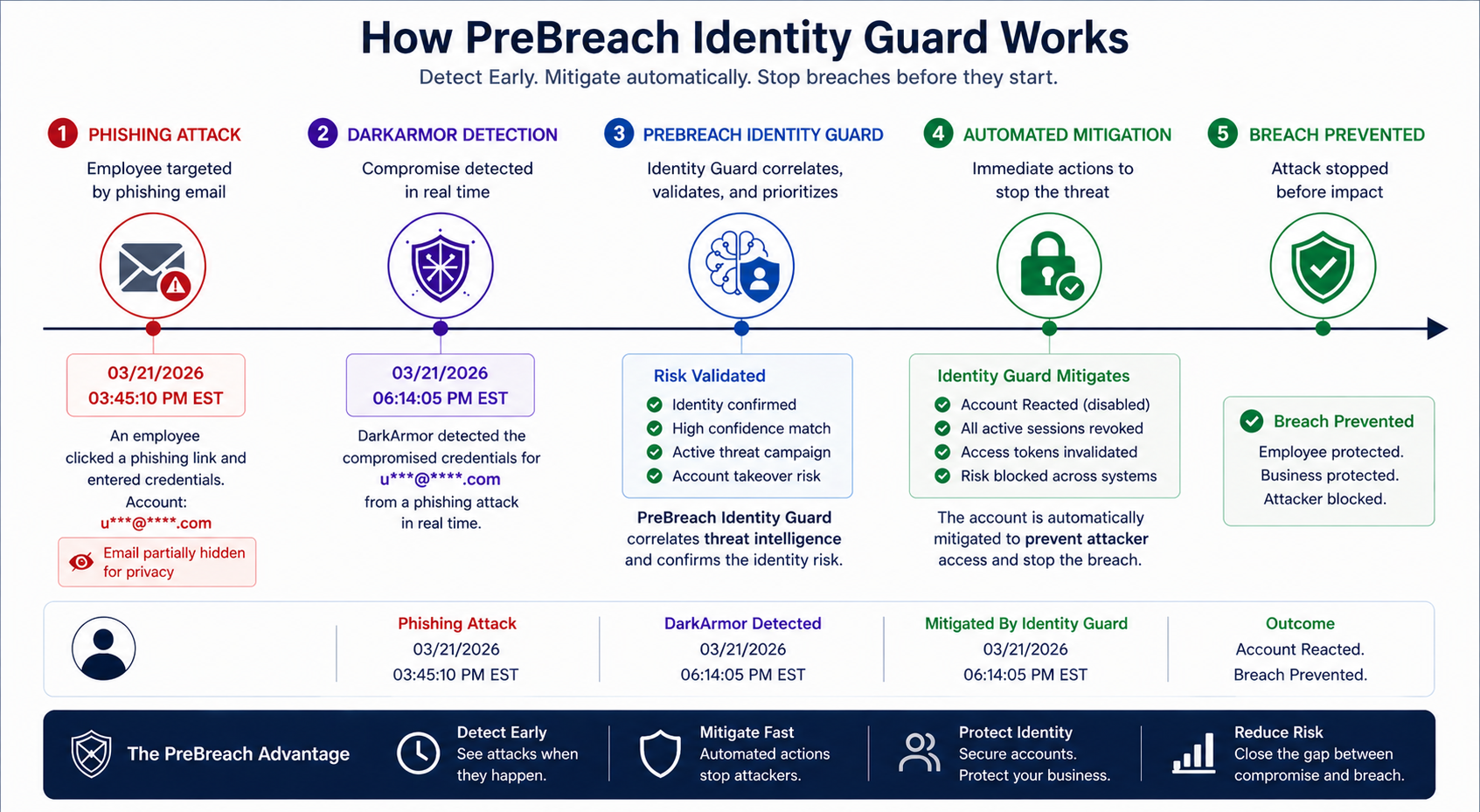
Figure 3: PreBreach Identity Guard Workflow
Final Thought
Cybersecurity is no longer about protecting systems alone. It is about protecting identities—before attackers use them.
PreBreach Identity Guard delivers:
- Early visibility
- Continuous monitoring
- Automated remediation
All powered by CyberArmor’s PreBreach intelligence.
Learn More
Explore how PreBreach Identity Guard can protect your organization:
https://cyberarmor.tech/solutions/prebreach-identity-guard
Want to detect threats 8+ months earlier?
See how DarkArmor's PreBreach intelligence can protect your organization.



