








Problem
Organizations operate in an environment of accelerating credential theft
The math is clear: early detection is not just better security — it is measurable financial protection.
$10.22 M
The average cost of a data breach in the USA in 2025, more than 2x the global average (IBM)
$900,000
Average savings when a breach is detected internally vs disclosed by an attacker (IBM)
+160%
Increase of credential theft due to AI powered phishing and malware-as-a-service (ITPro)
95%
Reduction in incident response time for MSSPs that use dark web monitoring (webz)
How it works
3 Steps to PreBreach Intelligence
We focus on your business and identify emerging threats before they impact your organization through continuous penetration and surveillance of underground forums in combination with proactive, autonomous methodologies.

1
Automated Data Collection
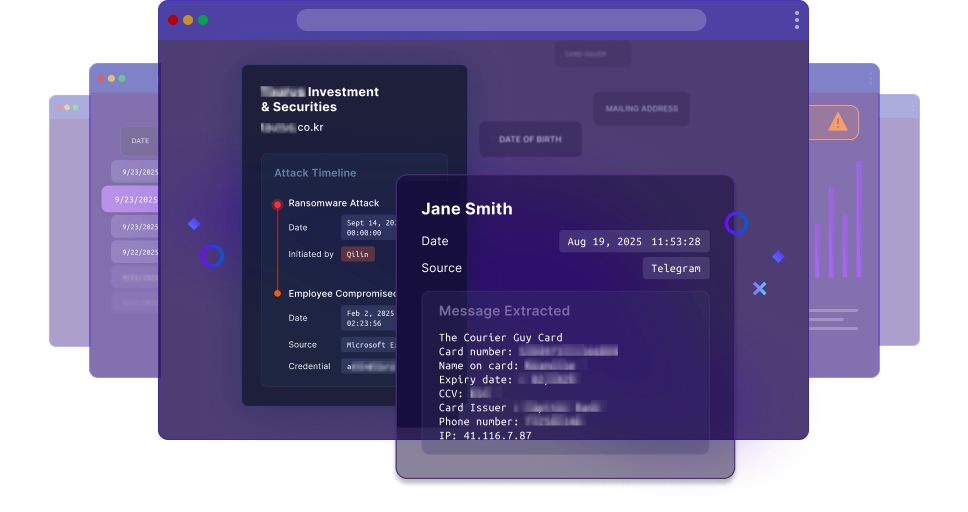
DarkArmor's proprietary engine continuously monitors active phishing campaigns and malware C2 infrastructure. When threat actors deploy phishing kits or operate infostealer malware, our systems intercept the data flow — extracting victim credentials from the infrastructure before the attacker processes them.

2
Asset Attribution and Analysis
Collected data is analyzed to identify which records belong to your organization. Compromised assets are matched against your monitored domains, email addresses, and custom queries. Data is normalized, deduplicated, and enriched with threat actor context.

3
Actionable Intelligence Delivered
Alerts reach you in real time through the DarkArmor platform, your existing SIEM (Splunk integration confirmed), or directly via our REST API. Every alert tells you what was compromised, when, how, and which attack led to the compromise.
Our Data
We Detect 8 Asset Types
Credentials
Email/password pairs, usernames, malware source. Passwords masked by default, audit-logged reveal.
Cookies
Browser cookies, session cookies, authentication tokens from compromised systems.
Access Tokens
Authentication tokens, session tokens, OAuth tokens from compromised systems.
Credit Cards
Payment card numbers (PAN), card brand, expiry. Last 4 digits only, CVV never exposed.
User PII
SSNs, phone numbers, addresses, full names. Masked by default (***-**-1234), audit logged.
Bank Accounts
Account credentials, financial account totals. Account numbers masked, financial exposure calculated.
Malware
Infected system data, screenshots, IOCs, stealer logs. Forensic evidence with secure viewing.
Fraudulent Checks
Stolen check images with OCR extraction. Visual review with PII warnings.
Our Differentiator
DarkArmor vs Traditional Dark Web Monitoring
Dimension
DarkArmor
Traditional Monitoring
Detection Timing
Before dark web listing
After dark web listing
Data Freshness
Real-time, pre-publication
Already public
Alert Lead Time
From days to months ahead
Weeks after listing
Method
Phishing and malware interception
Dark web scraping
Proactive Detection + Dark Web Monitoring
Our advanced forensics capture compromised credentials before it’s even sold on the dark web. When threat actors have the keys to your castle, it doesn’t matter how high your walls are or how wide your moat is.
+8 Months
Advance warning demonstrated
50,000
Fresh datapoints added daily
99.9%
Platform uptime
>5 min
Time to deply
Get PreBreach Protection
Get near real-time alerts when your organization’s credentials appear in data breaches or leaks...even before they’re exposed on the dark web.
Sign up for access
Advanced phishing and malware forensics to protect identity asset ownership before your organizations compromised credentials reach the dark web

Get proactive, prebreach intelligence

Be an early adopter with enhanced support and input on feature development

Limited time early adopter pricing

Get an edge over your competition

Get Our Report
Autumn Dragon: China-nexus APT Group Targets South East Asia
A China-nexus threat actor has been observed using a chain of DLL sideloading attacks to compromise government and media organizations across Singapore, Laos, Cambodia, Indonesia and the Philippines.
Download

