8+
Months Early Detection
Average advance warning before dark web listing.
99.9%
Detection Accuracy
Compromised credential intelligence collected from active threat sources.
$45K
Fraud Prevented
Single compromised check intercepted for a credit union.
8
Data Types Monitored
Credentials, Cookie, Access Token, PII, payment cards, checks, and more.
Our Difference
We provide focused intelligence about your organization's compromised identity assets
While other platforms are essential for defense, brand protection, and post-breach intelligence, we focus on the narrow but devastating window after a user is phished but before the stolen credentials cause damage. We do not just tell you that an attack happened; we tell you which employees are compromised and from which specific phishing or infostealer attack, allowing you to act before a breach occurs.
The PreBreach Window: Why Timing Matters
Traditional security tools detect threats after credentials hit the dark web. CyberArmor identifies compromise in the window where prevention is still possible.
How We Compare
We don't compete with these tools; we complement them by filling a critical blind spot
Our value lies in a unique dataset focused on pre-dark web compromised credentials-a source of intelligence that traditional threat intelligence and dark web monitoring platforms simply don't capture. While they analyze threats out in the world or inside your network, we show you the credentials being stolen from your employees right now, enabling a more complete and proactive security posture.

Specializes in dark web data collection and scraping, provides in-depth access to their data wholesale.
Use DarkOwl to get deep access and analysis of dark web data.

Our specialty is in identifying your compromises directly, whether they're on the dark web yet or not.
Use CyberArmor to identify specific credential theft on & before the dark web.

AI-driven internal network & email security; cloud-native forensics detects anomalous behaviour inside of your digital environment.
Use DarkTrace to monitor threats within your firewall.

We don't use AI or monitor inside your network-we monitor for your compromised identity assets out in the world.
Use CyberArmor to look for compromised identity assets outside your firewall.

Broad threat intelligence platform; analyzes the global cyber threat landscape for strategic insights.
Use Recorded future to analyze trends and patterns in the global threat landscape.

We focus on targeted, actionable intelligence on specific emails, domains, PII, etc rather than global trends.
Use CyberArmor to pinpoint specific compromises that put you at risk.

Protects against external threats such as brand impersonation, phishing, account takeover.
Use ZeroFox against external threats on public web and social media.

They protect your brand's public presence. We secure the private employee credentials behind it.
Use CyberArmor to have visibility on compromised assets & credentials.
Name
What They Do
What We Do

AI-driven internal network & email security; cloud-native forensics detects anomalous behaviour inside of your digital environment.
Use DarkTrace to monitor threats within your firewall.
We don't use AI or monitor inside your network-we monitor for your compromised identity assets out in the world.
Use CyberArmor to look for compromised identity assets outside your firewall.

Specializes in dark web data collection and scraping, provides in-depth access to their data wholesale.
Use DarkOwl to get deep access and analysis of dark web data.
Our specialty is in identifying your compromises directly, whether they're on the dark web yet or not.
Use CyberArmor to identify specific credential theft on & before the dark web.

Broad threat intelligence platform; analyzes the global cyber threat landscape for strategic insights.
Use Recorded future to analyze trends and patterns in the global threat landscape.
We focus on targeted, actionable intelligence on specific emails, domains, PII, etc rather than global trends.
Use CyberArmor to pinpoint specific compromises that put you at risk.

Protects against external threats such as brand impersonation, phishing, account takeover.
Use ZeroFox against external threats on public web and social media.
They protect your brand's public presence. We secure the private employee credentials behind it.
Use CyberArmor to have visibility on compromised assets & credentials.
The missing piece in your security stack
While other platforms excel in their respective areas, they often miss the critical window between when credentials are stolen and when they appear on the dark web

Early Visibility
We detect compromised credentials from infostealers and phishing campaigns before they are monetized or used in attacks.

Proactive Defense
By focusing on the pre-dark web phase, we enable you to reset passwords and secure accounts before they are abused, preventing account takeover and data breaches.

Actionable Intel
We don't just alert you to a breach; we tell you which employees are affected and which attacks led to the compromise, so you can take targeted action.
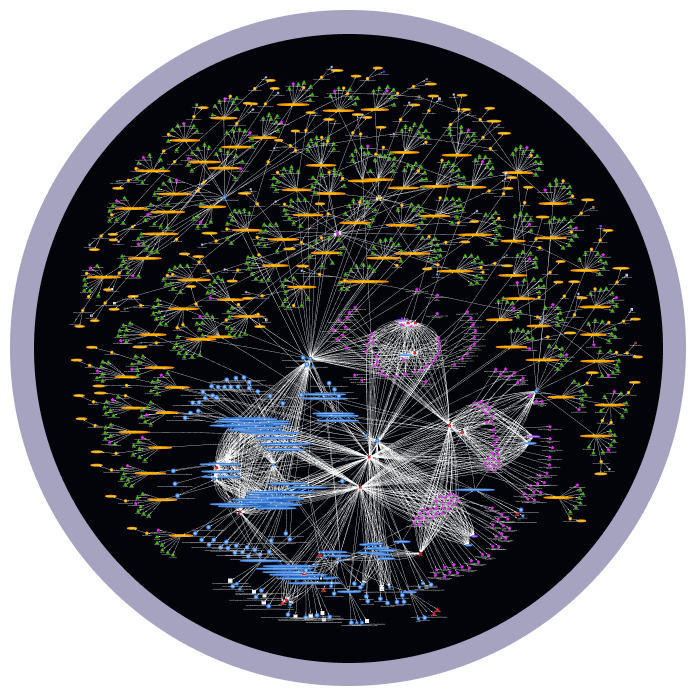
Connections That Matter
We analyze the connections between a cybercriminal, their campaign, and the victims they targeted
We don't just harvest raw information wholesale. We take steps to uncover the connections and behavioural patterns of a cybercriminal and highlight what matters to you.
Our platform finds key insights and actionable intel so that you and your organization can understand the behaviour of a threat actor and act to secure compromised credentials and identity assets.
Frequently Asked Questions
How is CyberArmor different from traditional dark web monitoring?
Traditional dark web monitoring only detects credentials after they've been posted on dark web forums and marketplaces, often months after initial theft. CyberArmor detects compromised credentials from infostealers and phishing campaigns within days, before they reach the dark web.
How far in advance can you detect compromised credentials?
On average, we detect compromised credentials 8+ months before they appear on the dark web. In many cases, we identify them within days of the initial phishing or infostealer attack.
What types of credentials and data do you monitor?
We monitor eight primary data types including email and password pairs, cookies, access tokens, PII, payment card data, financial account credentials, infostealer system artifacts, and stolen check images.
Do you monitor inside my network like EDR or SIEM tools?
No. We do not replace network monitoring tools. CyberArmor monitors compromised identity assets in the prebreach phase outside your firewall, complementing your existing EDR, SIEM, and SOC workflows.
How does this integrate with my existing security stack?
CyberArmor is built to complement your stack by filling the gap between internal detection tools and dark web monitoring. For Azure environments, PreBreach Identity Guard supports rapid protection and remediation workflows.
Can you identify specific employees who are compromised?
Yes. We provide user-level attribution and link specific compromised credentials to associated phishing or infostealer activity so your team can take targeted action.
How quickly can I start protecting my organization?
Book a personalized demo to scope monitored assets, review use cases, and align remediation workflows with your security team.
What industries do you serve?
CyberArmor supports organizations across finance, education, retail, government, and healthcare, especially teams concerned with credential theft and account takeover risk.
Sign up for access
Advanced phishing and malware forensics to protect identity asset ownership before your organizations compromised credentials reach the dark web

Get proactive, prebreach intelligence

Be an early adopter with enhanced support and input on feature development

Limited time early adopter pricing

Get an edge over your competition