Overview
Recent phishing activity shows a shift toward modern web application architectures, from email base to telegram, to man-in-the-browser. And now, a Gmail-themed phishing page was observed using GraphQL for credential submission, while sitting behind Cloudflare to reduce detection and infrastructure exposure.
This approach blends into legitimate traffic patterns and complicates traditional security controls.
Attack Flow
1. User Delivery
The victim receives a phishing email directing them to a Gmail-branded login page. In the recent incident we investigated, the attacker used a voice message email theme to socially engineer the user into opening the phishing link. Figure 1 shows a screenshot of the phishing email.
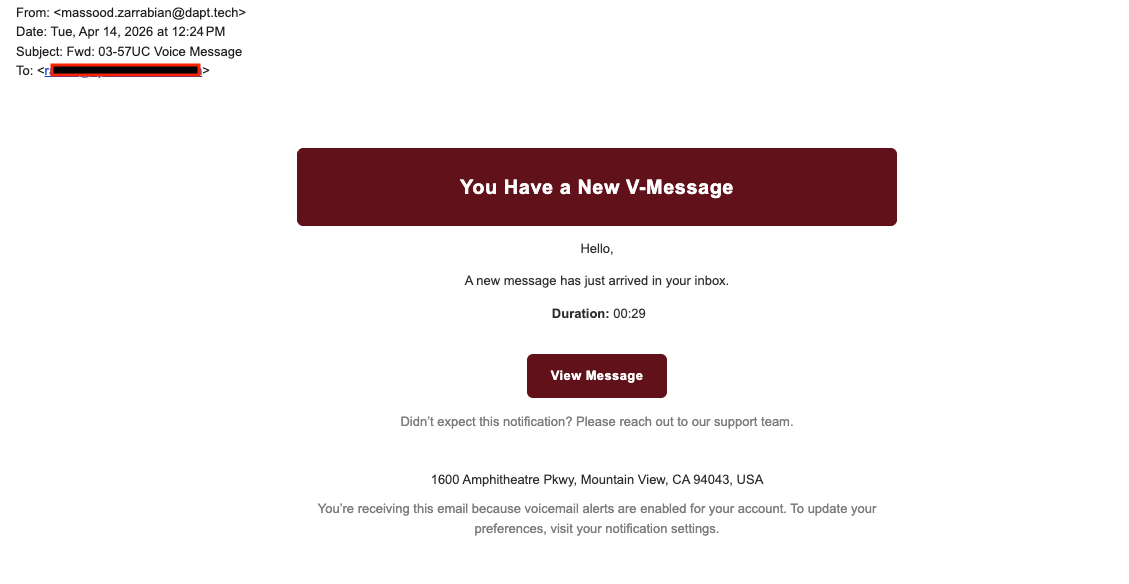
Figure 1: Fake Voice Message Phish
2. Phishing Landing Page – Fake “New Voice Message” Page
Once the user clicks View Message in the email, they are redirected to a website that pretends to host a new voice message. Figure 2 shows a screenshot of the landing page.
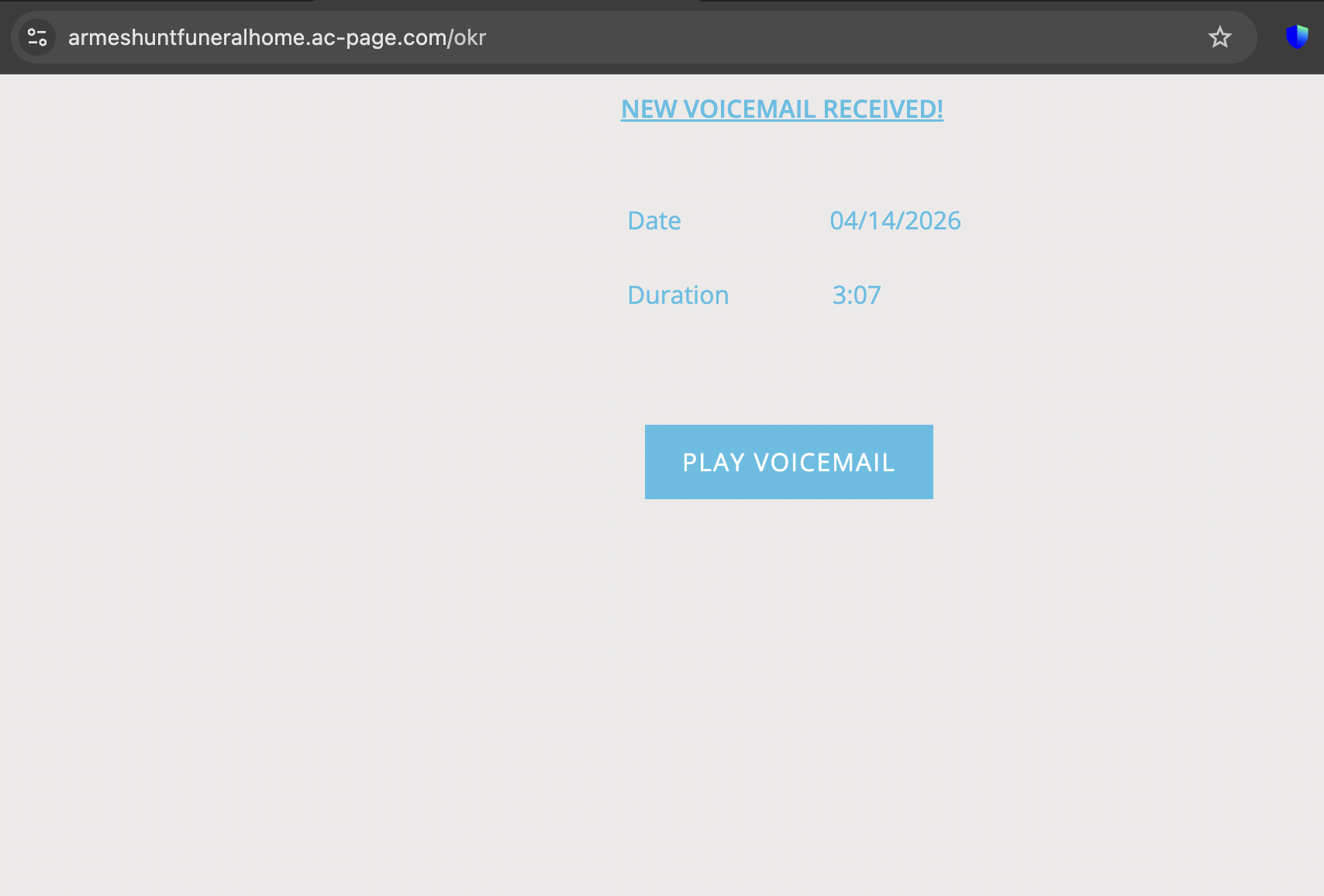
Figure 2: Fake Voice Message Landing Page
3. Gmail-Themed Interface
Once the user clicks “Play Voicemail,” they are prompted to complete a basic reCAPTCHA to reduce automated detection. After passing the check, the page redirects to voicemsgirdhan170coj.gotech-ae[.]com. The page closely mimics Gmail, including layout, fonts, and interaction flow. Figure 3 shows a screenshot of the phishing page.
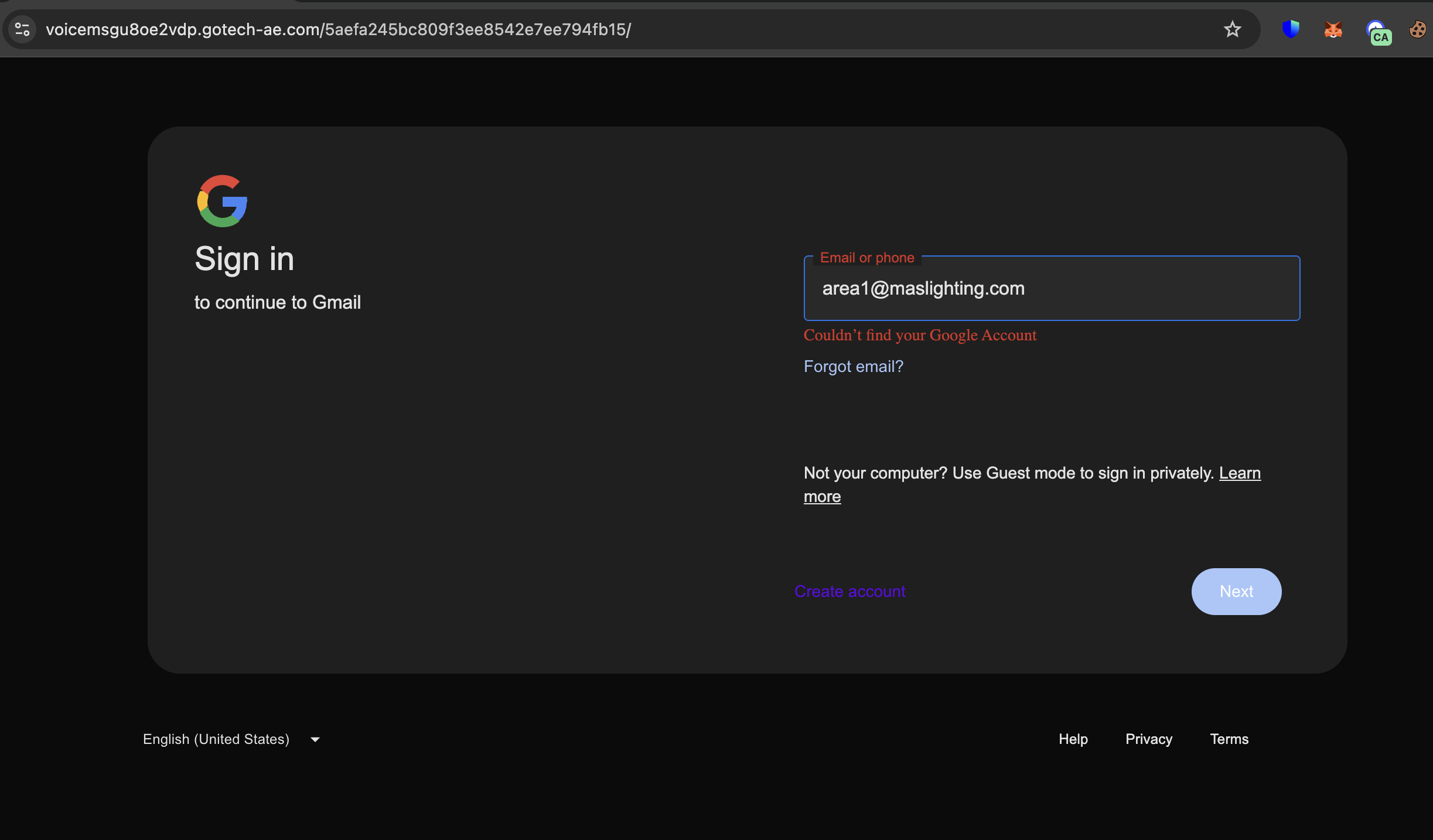
Figure 3: Gmail Phish Page
4. GraphQL Submission
Once the user accesses the phishing page and begins submitting credentials, the data is sent to the GraphQL server via a GraphQL mutation, as shown below.
{
"query":"
mutation Submit($sessionId: String!, $value: String!, $secondaryButton: Boolean) {
submitInput(sessionId: $sessionId, value: $value, secondaryButton: $secondaryButton)\n }
",
"variables":{
"sessionId":"4af6c8338b7c4ca99e3d965de346b344",
"value":"hackme@gmail.com"
},
"operationName":"Submit"
}
Once the email is submitted, the next page displays a password input field, mirroring the Gmail login flow. Figures 4 and 5 show screenshots of the network activity during the submission of the user’s email and password.
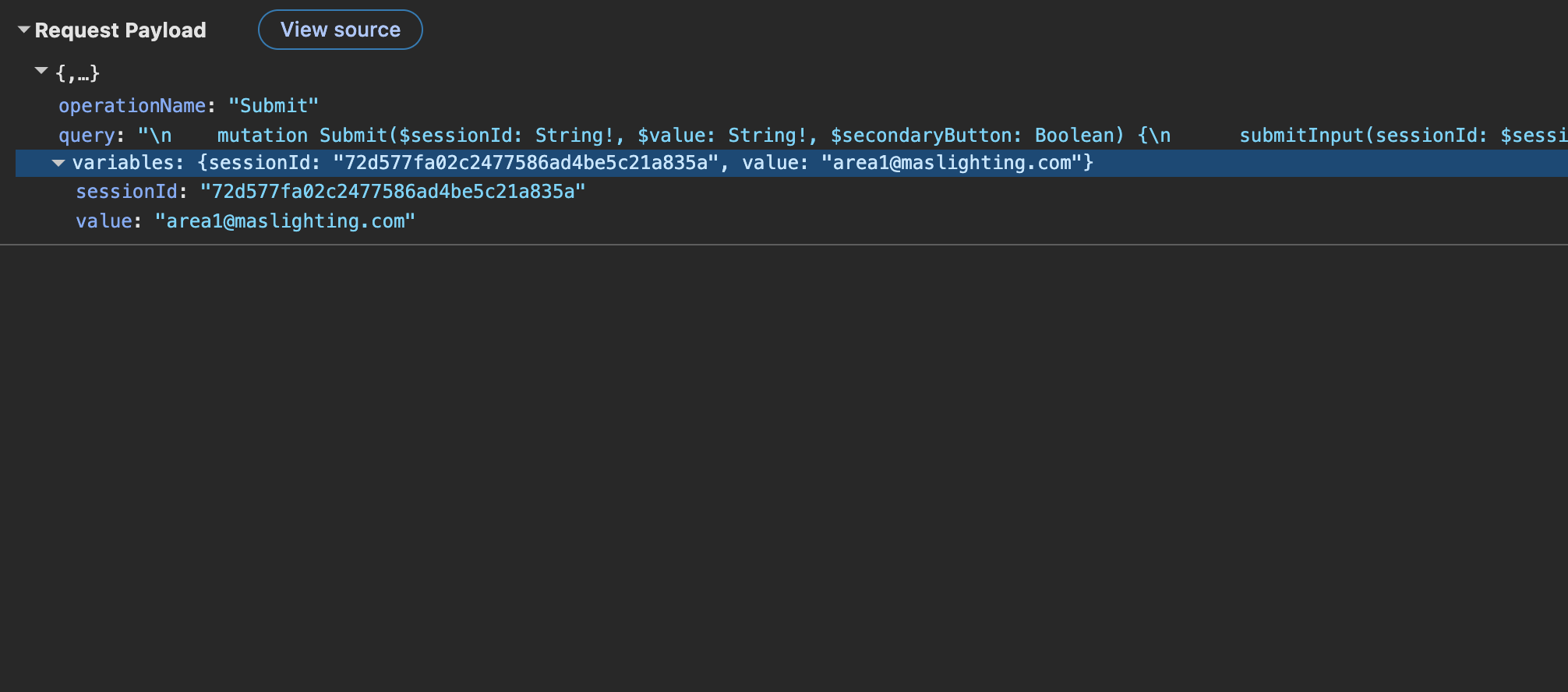
Figure 4: Submit Email To Phish Server
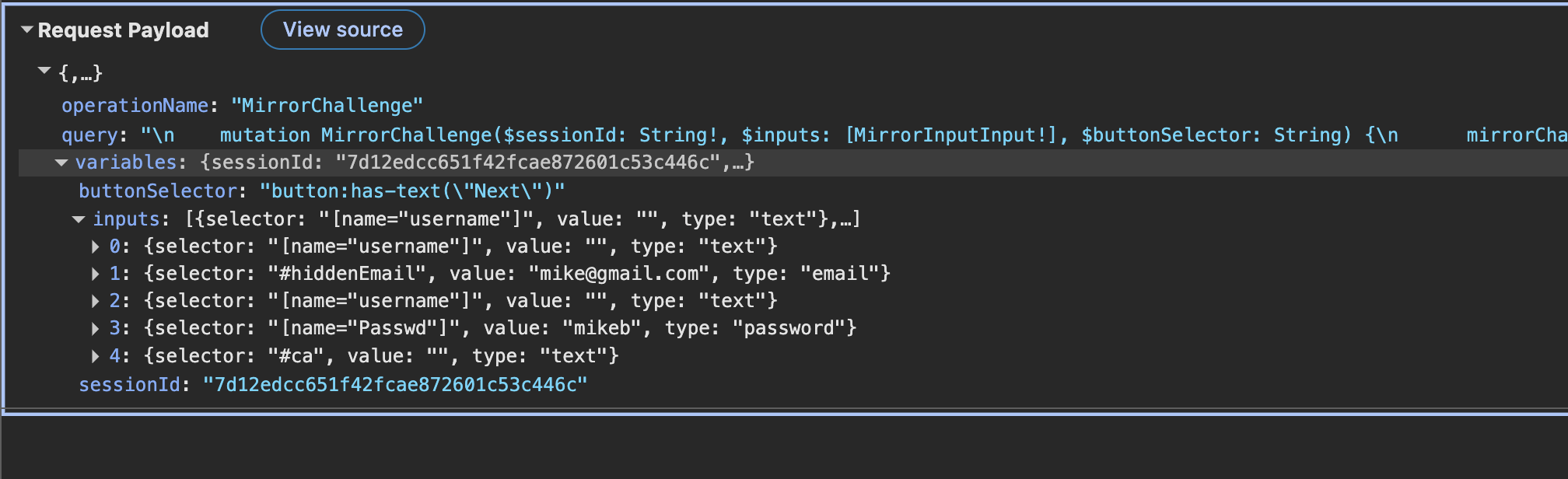
Figure 5: Submit Password
GraphQL Phish Framework
In this phishing campaign, instead of a standard POST request, credentials are submitted via a GraphQL mutation. A GraphQL mutation is an operation used to modify data on a server—such as creating, updating, or deleting information—using GraphQL. By leveraging this technique, the phishing workflow introduces an additional layer to its communication.
Furthermore, the attacker can use GraphQL resolvers to validate credentials in real time on the server side. Unlike tools such as Evilginx and other man-in-the-browser phishing frameworks, this approach performs validation entirely on the backend and does not return meaningful results to the client. Session data and cookies remain on the server, reducing exposure on the client side.
Using GraphQL-based credential harvesting offers a different tradeoff compared to Evilginx (MITB/reverse proxy). The advantages are mainly operational simplicity and lower exposure, not necessarily capability.
Key benefits over Evilginx
- No need to proxy a live target site
- No certificate spoofing or session relay
- Simple backend API (e.g.,
/graphql) handles everything
Reduced detection surface
- No real-time proxying of a legitimate domain (common detection point for Evilginx)
- Traffic looks like a normal API call rather than full page mirroring
- Easier to hide behind CDN/WAF (e.g., Cloudflare)
More resilient to takedown
- Backend is decoupled from the phishing UI
- GraphQL endpoint can be reused across multiple phishing pages
- Faster to rotate frontend domains while keeping backend intact
Flexible data handling
- Structured credential capture (JSON)
- Easy to extend (add MFA, tokens, device info) without changing endpoints
Server-side validation control
- Attackers can validate credentials in real time via backend logic
- Can suppress responses or simulate errors without exposing real target interaction
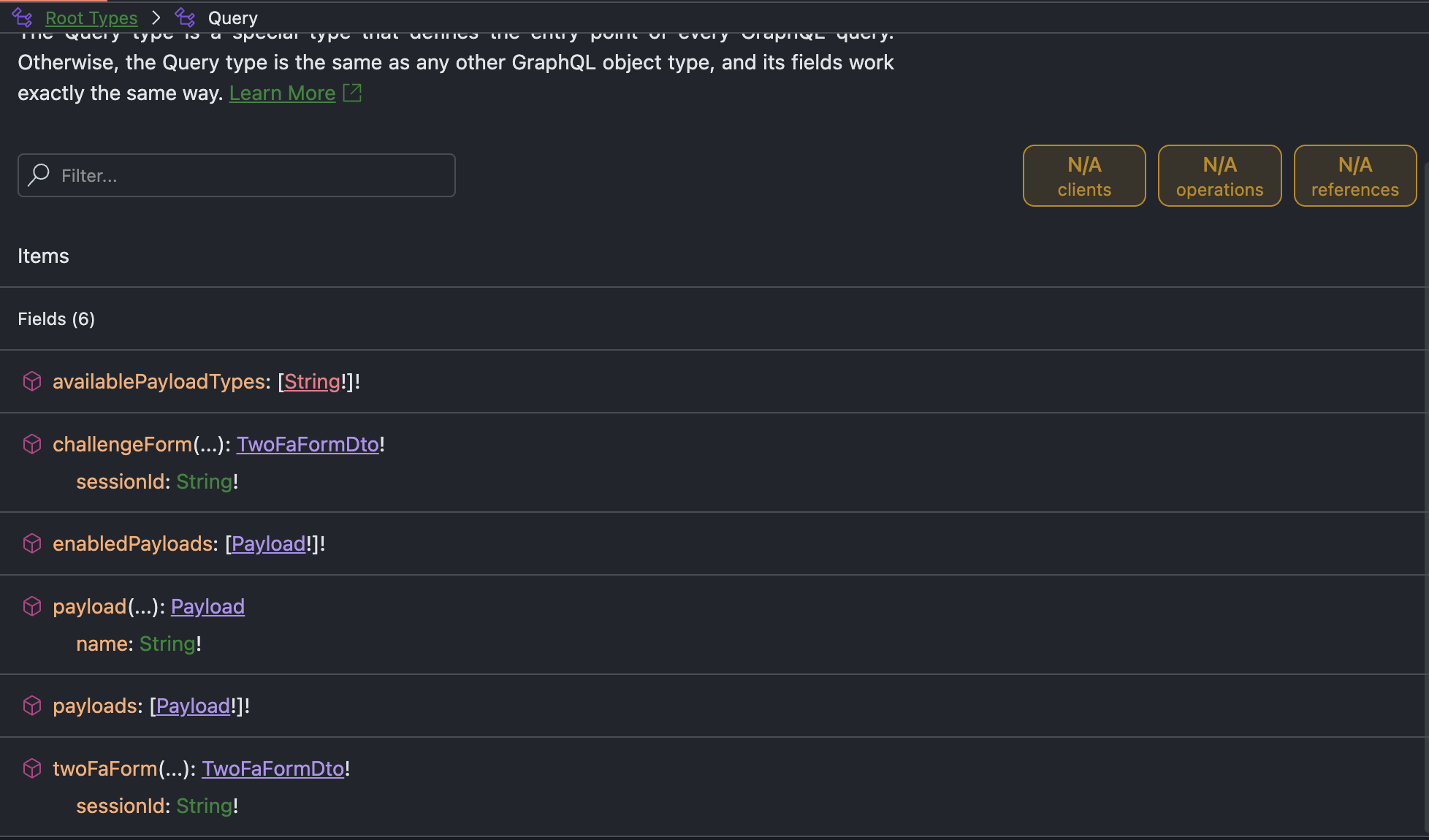
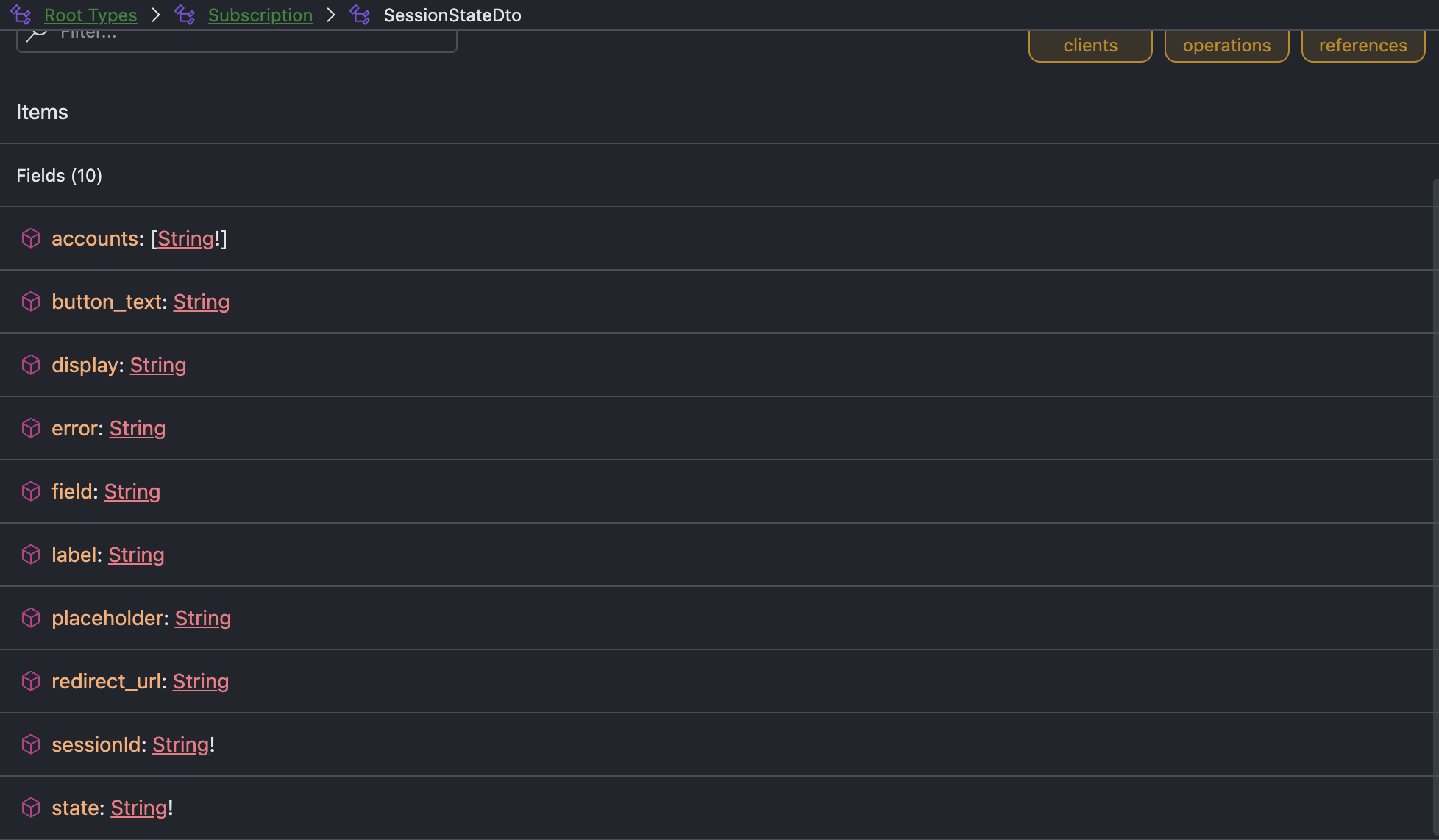
Infrastructure
The GraphQL server is run on Nitro platform from chillicream.com. The platform enable the user to query and view the schema of the GraphQL as shows in the following.
Conclusion
This campaign demonstrates how phishing continues to evolve by adopting modern web technologies. By combining a Gmail-themed interface, GraphQL-based credential submission, and infrastructure protection through Cloudflare, the attacker reduces traditional detection signals while maintaining operational efficiency.
The use of GraphQL is particularly notable. It allows structured data collection, flexible backend logic, and real-time validation without exposing interaction details to the client. This shifts phishing further away from simple form-based exfiltration toward API-driven workflows that blend with legitimate application traffic.
Defenders should not rely solely on indicators such as page appearance or known endpoints. Instead, detection must evolve to include behavioral analysis, API-level inspection, session monitoring, and Proactive Intelligence. As attackers continue to align their techniques with modern architectures, visibility into how data is transmitted—not just where—is becoming critical.
IOCs
hxxps://armeshuntfuneralhome.ac-page[.]com/okr
hxxps://arnco-est[.]com/voicemp3
hxxps://voicemsgirdhan170coj.gotech-ae[.]com/
Want to detect threats 8+ months earlier?
See how DarkArmor's PreBreach intelligence can protect your organization.



