The Landscape: A Post-Banking Economy
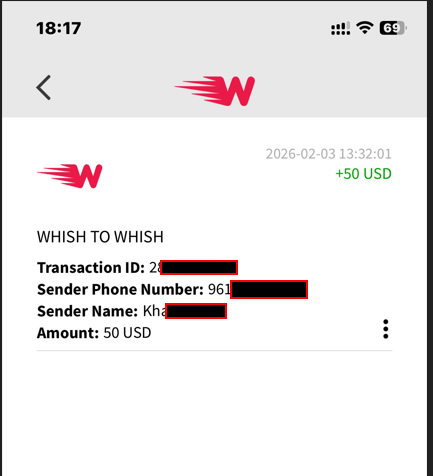
By 2026, the Levant operates in a state of financial collapse. Lebanese bank deposits remain frozen, while the Syrian pound continues to fluctuate sharply. In response, the region has shifted toward a decentralized, mobile-first financial ecosystem. Services such as Whish Money now function as critical remittance infrastructure, effectively replacing traditional banking channels.
Operation Gauloises demonstrates how this infrastructure is being repurposed. The same speed and trust that make these platforms viable lifelines also make them vulnerable. Illicit actors exploit them to move high-risk capital across borders with minimal traceability.
The Mask: The Tartous Ramadan Front
The operation is fronted by a localized, religious-themed web portal designed to appear legitimate. The “Ramadan of Goodness” campaign is not a phishing mechanism; rather, it serves as a behavioral shield. By framing transactions as charitable contributions, it normalizes unusually high volumes of inbound peer-to-peer transfers.
This “retail mask” functions as a public-facing storefront. The religious framing provides social and cultural cover, allowing hundreds of incoming payments to appear routine rather than suspicious.
The Retail Mask. This page serves as the public "storefront." By framing the sale of stolen goods as a religious campaign, the operator justifies hundreds of inbound Whish transfers as "charitable contributions."
The Asset: Liquidation of Stolen Netflix & Shein Cards
At its core, the operation revolves around the resale of stolen digital gift cards. These assets are not acquired through direct phishing of end users but sourced from broader fraud ecosystems. They are then resold locally at discounted rates to ensure rapid turnover.
The pricing structure reflects a deliberate arbitrage strategy (e.g., a $30 card sold for $25). This discount incentivizes buyers while enabling the operator to convert compromised digital assets into usable local currency.
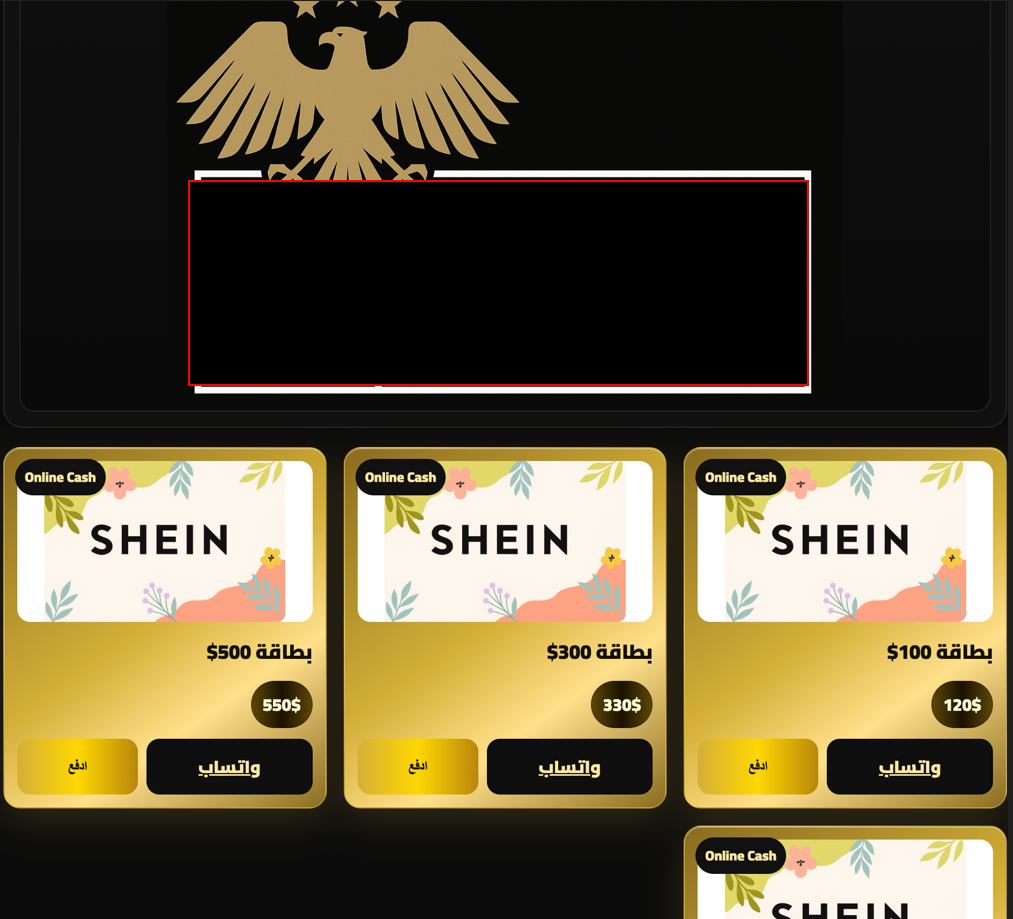

The Product. Stolen Netflix and Shein cards sold at "Grey Market" rates. Note the pricing (e.g., $30 value for 25$). This arbitrage is how the operator turns global "hot" cards into "clean" local USD credits.
The Bridge: The "Blind" Whish Money Rail
Whish Money functions as an opaque clearing layer within the scheme. From the platform’s perspective, transactions appear as standard peer-to-peer transfers.
- Sale: A buyer purchases a discounted digital card through the portal.
- Transfer: Payment is sent via Whish Money to the operator.
- Obfuscation: The platform records a routine remittance, with no visibility into the illicit origin of the underlying asset.
This separation effectively disconnects the fraudulent source from the financial endpoint. By the time funds are received, they appear legitimate within the system.
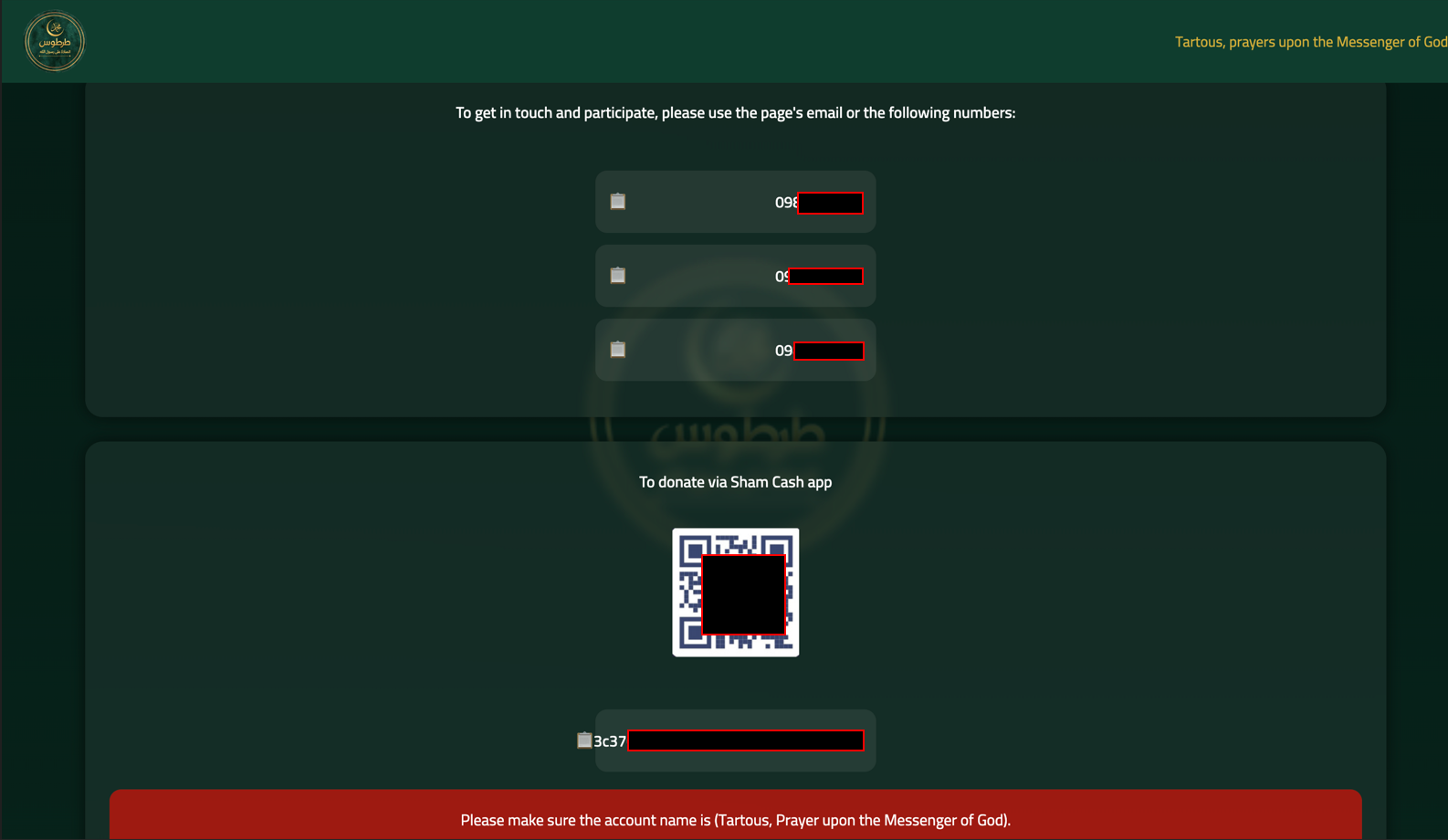
The Payment Rail. Sham Cash and Whish Money accounts facilitate the instant conversion of stolen assets into spendable local currency.
The Operator: The "Gauloises" Tradecraft
The operation is managed through a conventional hosting environment, using a localized administrative interface. This suggests a technically competent regional actor rather than an ad hoc participant.
The backend functions as an inventory and transaction hub, tracking both the supply of stolen cards and the flow of incoming payments. Operationally, the actor behaves as a broker—facilitating the conversion of global fraud outputs into localized liquidity.
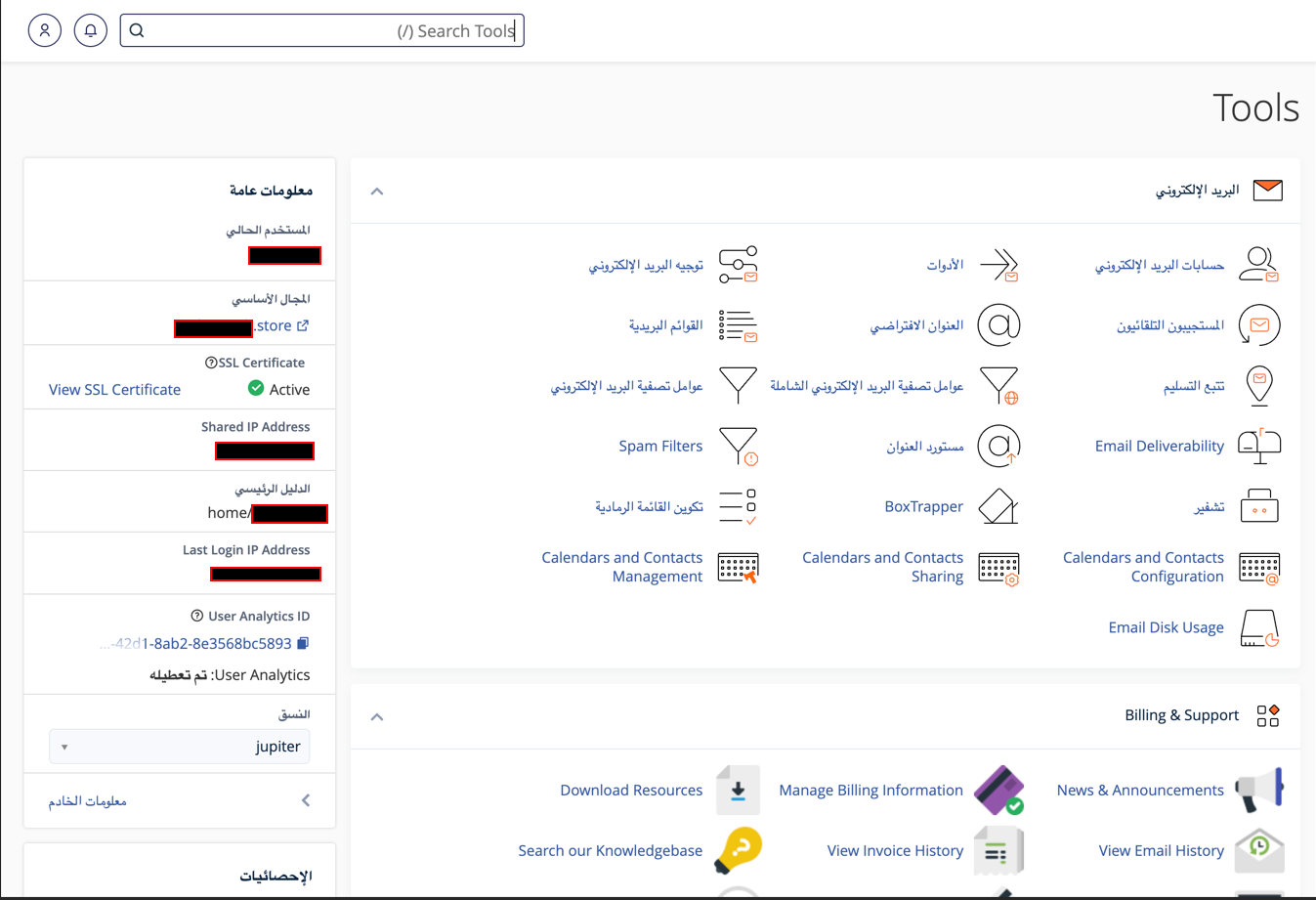
The Inventory Manager. This is the command center where the operator manages the stock of stolen cards and monitors the incoming "donations" on the Whish rail.
The Face of Operation Gauloises
The operator maintains a minimal physical and digital footprint, embedded within the rhythms of everyday life in the Levant. He works from cafés where time moves slowly—spaces defined by strong coffee, constant cigarette smoke, and long, unhurried conversations. These environments are not incidental; they provide both anonymity and cover. Transactions are managed quietly from a phone or laptop, indistinguishable from routine social or business activity.
In this setting, high transaction volume does not appear anomalous. The culture of informal exchange, cash fluidity, and dense social networks normalizes constant financial movement. The operator’s advantage lies not in advanced technical concealment, but in his ability to operate within these familiar patterns—leveraging trust, ambient noise, and the relaxed cadence of daily life to obscure a structured, high-throughput illicit workflow.

Conclusion: The Unreachable Rail
Operation Gauloises proves that the most dangerous financial threats are those that use the system exactly as it was designed. By the time a "donation" is cashed out at a Whish Money agent, the stolen card has already been redeemed, and the money is "clean." The "cigarette guy" remains invisible, his trail ending in a cloud of Gauloises smoke and a neutral fintech ledger.
Want to detect threats 8+ months earlier?
See how DarkArmor's PreBreach intelligence can protect your organization.



